The industrial automation landscape has undergone a seismic shift in recent years, driven by the convergence of operational technology (OT) and information technology (IT). At the heart of this transformation lies a critical yet often overlooked component: the protocol converter bridging PLCs and IT systems. These unassuming gatekeepers enable legacy manufacturing equipment to speak the language of modern enterprise software, creating opportunities for data-driven decision-making that were previously unimaginable.
The protocol translation challenge emerges from fundamentally different design philosophies. Programmable Logic Controllers (PLCs) were built for deterministic real-time control, using specialized industrial protocols like Modbus, Profibus, or DeviceNet. Meanwhile, IT systems operate in the realm of TCP/IP, REST APIs, and SQL databases. The converter must not merely translate messages but reconcile these opposing worlds - maintaining the millisecond response times required by industrial processes while providing the abstraction layer needed for business system integration.
Modern protocol converters have evolved beyond simple signal translators. The latest generation incorporates edge computing capabilities, allowing for data preprocessing before transmission to higher-level systems. This architectural approach reduces network load and enables local decision-making for time-sensitive operations. A converter might aggregate minute-level sensor readings into meaningful hourly production metrics while simultaneously streaming critical alarm conditions in real-time to a SCADA system.
Industrial environments present unique challenges that commercial IT equipment cannot withstand. Protocol converters designed for factory floors feature ruggedized enclosures, wide operating temperature ranges, and immunity to electromagnetic interference. These physical characteristics often prove as crucial as the software functionality, especially in industries like metal processing or petrochemicals where environmental conditions would destroy standard networking gear within months.
The cybersecurity implications of PLC-IT bridging cannot be overstated. Every protocol converter represents a potential attack surface that could allow malicious actors to penetrate deep into industrial control systems. Leading manufacturers now build in features like role-based access control, encrypted communications, and detailed audit logging. Some even incorporate anomaly detection algorithms that can identify and block suspicious traffic patterns before they reach sensitive control equipment.
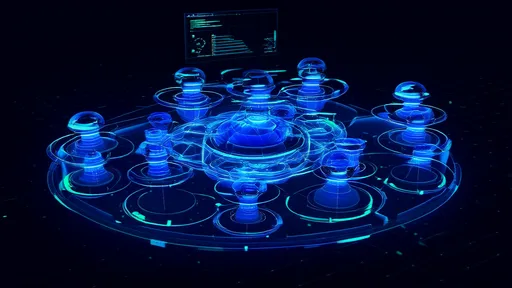
Implementation considerations vary dramatically based on the scale and complexity of the automation environment. Small manufacturers might deploy standalone converters for individual machines, while large process plants often require rack-mounted modular systems capable of handling hundreds of simultaneous protocol translations. The most sophisticated implementations use distributed architectures with converters deployed at multiple levels of the automation pyramid, each optimized for its specific position in the data flow hierarchy.
Looking ahead, the role of protocol converters will continue evolving alongside industrial IoT (IIoT) advancements. Emerging standards like OPC UA over TSN (Time-Sensitive Networking) promise to reduce - but not eliminate - the need for protocol translation. Even as newer equipment adopts these unified standards, the vast installed base of legacy industrial systems ensures that converters will remain essential components of manufacturing IT infrastructure for decades to come.
The true measure of a successful PLC-IT protocol converter lies in its invisibility. When functioning optimally, these devices disappear into the infrastructure, creating seamless data flows that empower organizations to optimize production, predict maintenance needs, and respond dynamically to changing market conditions. In an era where manufacturing competitiveness increasingly depends on data agility, the humble protocol converter has become an unsung hero of the smart factory revolution.

By /Jul 22, 2025

By /Jul 22, 2025

By /Jul 22, 2025

By /Jul 22, 2025

By /Jul 22, 2025

By /Jul 22, 2025

By /Jul 22, 2025
By /Jul 22, 2025
By /Jul 22, 2025

By /Jul 22, 2025

By /Jul 22, 2025
By /Jul 22, 2025

By /Jul 22, 2025
By /Jul 22, 2025
By /Jul 22, 2025

By /Jul 22, 2025

By /Jul 22, 2025

By /Jul 22, 2025